Curated by
November 21, 2025
-
December 16, 2025
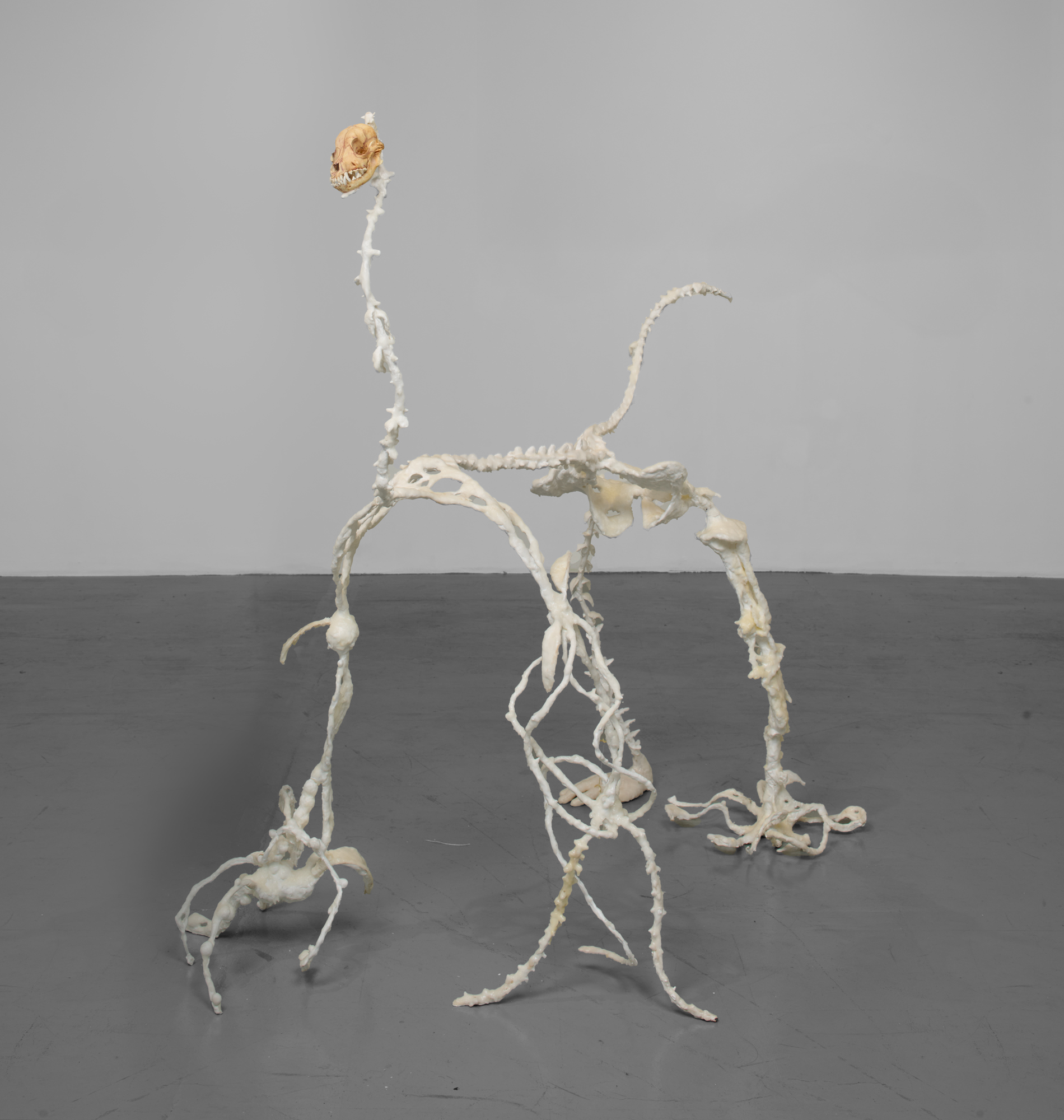
Image: Hyunjin Park, 'Three Bodies of Cerberus', 2024. Photographed by KC Crow Maddux. Engine Spoofer 2.0.5.rar
The deep lore surrounding this specific version involves a phenomenon users called
It first appeared on a private hardware-ID (HWID) spoofing board in late 2023, posted by a user named ’NullReference’ . Unlike standard spoofers that simply mask your motherboard or disk serials to bypass game bans, version 2.0.5 claimed to operate at the —essentially running beneath the operating system itself, within the CPU’s microcode instructions. The Legend of the "Mirror"
By the time the developers of the original tool scrubbed all mentions of 2.0.5 from their site (jumping straight to version 2.1.0), the "2.0.5.rar" had become a digital cursed object. Some say the code was an experimental "digital twin" project that leaked, designed to see if a machine could exist in two places at once. The Warning
And eventually, someone else might start using identity to log in.
As the .rar file was mirrored across public sites, the story took a darker turn. Users began noticing that after using 2.0.5, their BIOS screens would occasionally flicker with strings of text that weren't part of the manufacturer's code. It wasn't malware in the traditional sense—nothing was stolen, and no files were deleted. Instead, the hardware seemed to be "forgetting" what it was.
Legend has it that 2.0.5 didn’t just generate random serial numbers; it "borrowed" them. Within hours of running the executable, users reported that their original hardware IDs weren't just hidden—they were being seen "active" on servers in different hemispheres. One famous (though unverified) post claimed a user found their unique PC signature logged into a high-security corporate network in Seoul while they were sitting in a basement in Ohio. The Corruption